In an age where data breaches and cyber-attacks are becoming increasingly commonplace, the importance of software security testing cannot be overstated. Ensuring the security of software applications is not just a technical requirement,but a business imperative. However, navigating the landscape of software security can be akin to traversing a minefield. This article aims to shed light on the diverse approaches, tools, and types of software security, offering you an in-depth look into this critical facet of the software development life cycle.
Understanding the Essentials of Software Security Testing
In essence, what is security testing? The term often mystifies many, leaving them perplexed about its scope and purpose. Software security testing refers to a process designed to identify vulnerabilities, risks, and weaknesses within the software application. It’s more than just a checkbox on a to-do list; it’s a rigorous methodology aimed at ensuring the software’s reliability and trustworthiness.
Security testing in software testing is not isolated to a single phase, but should be integrated throughout the software development lifecycle. This proactive approach minimizes risks and allows for easier identification and mitigation of security flaws.
A proper software security assessment involves various stakeholders, from developers and QA testers to security experts. All parties contribute their expertise to scrutinize the software from multiple angles, ensuring a comprehensive evaluation.
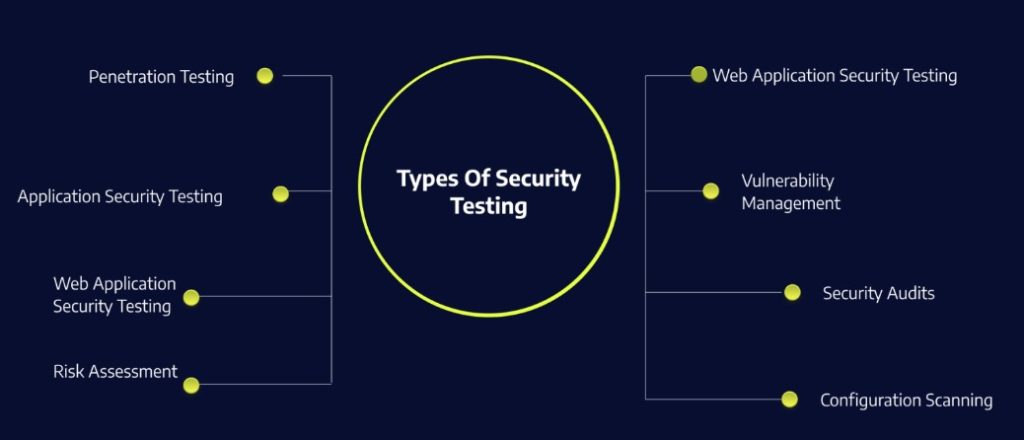
Different types of software security testing include static analysis, dynamic analysis, and penetration testing. Each offers unique insights into different facets of software security and, when employed in tandem, can provide a robust security posture.
Why does software security testing matter? In the absence of adequate security measures, the integrity of an application is compromised. Risks such as data breaches, financial loss, and reputational damage become inevitable, affecting both businesses and end-users.
Approaches to Security Testing
A one-size-fits-all approach rarely works in the context of software security assessment. Organizations must adapt and tailor their strategies based on specific needs and constraints.
For instance, Agile and DevOps methodologies prioritize quick iterations and continuous delivery. This necessitates an approach to security testing in software testing that’s both iterative and integrated, capable of keeping pace with rapid development cycles.
Risk-based testing, on the other hand, focuses on the most critical parts of an application. This targeted approach prioritizes the areas most susceptible to attack or failure, directing resources efficiently.
When considering how to do security testing, automation can’t be ignored. Automated testing tools are efficient and effective, especially for recurring tests and large codebases. However, manual testing plays a complementary role, uncovering issues that automated tests may overlook.
Gray-box testing, a hybrid approach, uses a combination of both white-box and black-box testing techniques. It leverages limited knowledge of an application’s internal structure, enabling a more nuanced and comprehensive assessment.
There’s also a need for a multi-layered approach. System security testing verifies the system’s overall security mechanisms, while data security testing focuses on protecting the data that the application handles.
Types of Software Security
Understanding the different types of software security is vital for a well-rounded security posture. At the application level, application security testing focuses on the software’s source code and architecture, scrutinizing it for vulnerabilities that could lead to unauthorized access or data leakage.
Infrastructure security ensures that the underlying systems where the software is deployed are secure. It incorporates network security measures, firewalls, and intrusion detection systems, to name a few.
Data security testing aims at safeguarding the data processed or stored by the application. This includes encrypting data at rest and in transit, and implementing strong access controls.
It’s also imperative to secure the interfaces that the software interacts with. This is often achieved through API security testing, validating that data exchanges between different software components are secure.
Lastly, end-point security focuses on the devices that interact with the software. This can range from servers and workstations to mobile devices, each with its unique security considerations.
Tools for Effective Software Security Testing
It would be remiss to talk about security testing without highlighting some prominent software security testing tools that empower organizations to bolster their security protocols.
Dynamic Application Security Testing (DAST) tools, such as OWASP ZAP and Burp Suite, analyze running applications for real-time vulnerabilities. They simulate attacks and assess the application’s response mechanisms.
Static Application Security Testing (SAST) tools like Checkmarx and Fortify scrutinize the application’s source code for potential vulnerabilities. They are especially useful for identifying issues early in the development process.
For those focused on infrastructure, tools like Nessus and OpenVAS offer comprehensive vulnerability assessments. These tools are vital for system security testing, providing insights into potential weak spots within the system architecture.
When it comes to IT-security testing, tools like Metasploit offer penetration testing capabilities. They simulate cyberattacks to evaluate the robustness of your security defenses.

Future Trends and Best Practices
In the ever-evolving landscape of software security, staying ahead of emerging threats is a constant challenge. Zero-day vulnerabilities, advanced persistent threats, and increasingly sophisticated cyber-attacks make software security testing more crucial than ever.
Adopting a DevSecOps approach, which integrates security into every stage of the software development lifecycle, is fast becoming the norm. This enables continuous security testing in software testing, ensuring that security is an ongoing process rather than a one-off task.
Security champions are another emerging trend. These are individuals within development teams who take the lead in advocating for security best practices. They serve as the bridge between developers and security teams, enhancing the overall security culture within an organization.
Cloud-based security solutions are gaining traction, offering scalability and flexibility that on-premises solutions often lack. They enable real-time monitoring and offer automated updates, ensuring that the latest security features are always at hand.
Conclusion
The vitality of software security testing can never be overstated. It is an indispensable practice for organizations that want to safeguard their assets, protect customer data, and maintain a strong reputation. A multi-faceted approach, employing various types of testing and a range of tools, is crucial for a robust software security posture. As technology continues to evolve, so will the challenges and methodologies associated with software security. Thus, it is imperative for organizations to stay vigilant, adaptable, and ever-prepared for the changing security landscape.